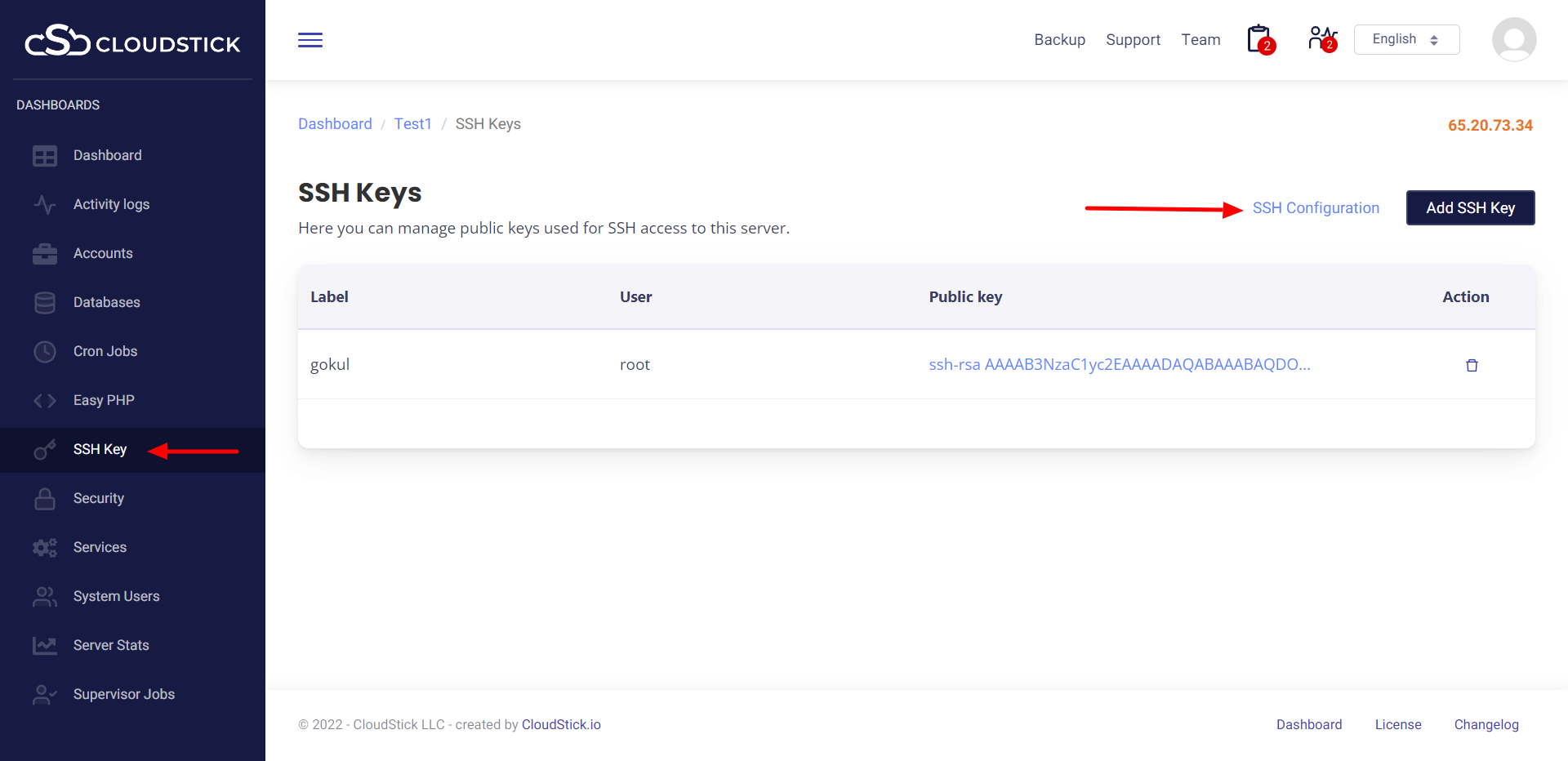
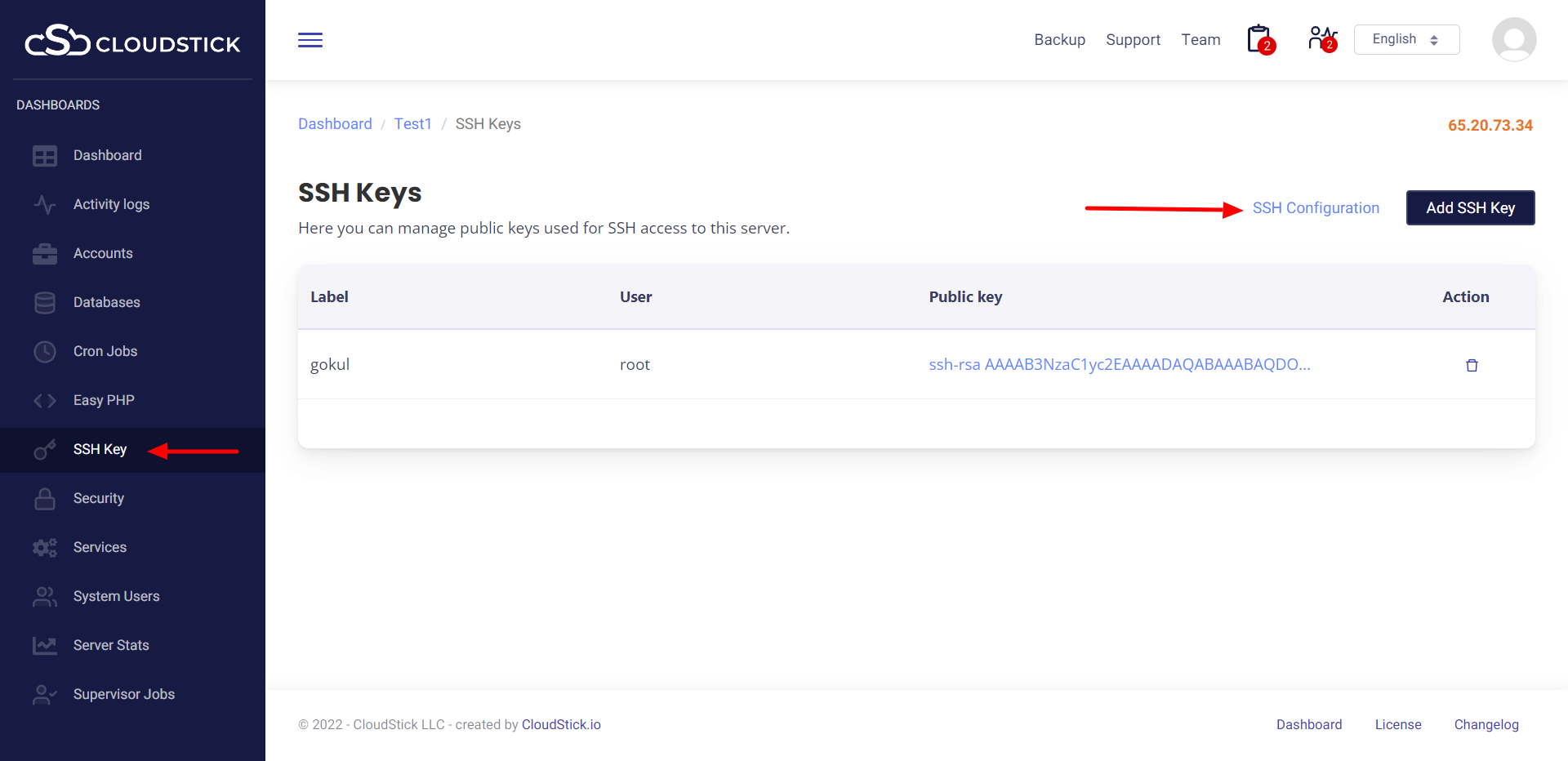
You can secure SSH access by enabling key authentication and preventing root access. You can do this in CloudStick using SSH Config.
"Explore CloudStick: Your Ultimate Guide to Mastering Cloud Management" - Dive into tutorials, tips, and insights on leveraging CloudStick for efficient server management, automation, and security across multiple cloud platforms, tailored for developers and businesses.
You can secure SSH access by enabling key authentication and preventing root access. You can do this in CloudStick using SSH Config.